Digital Forensic with AI 101 - Corporate Espionage by NS and DNS manipulation

Leadership Series
Let's begin with something different! From the title you can probably tell this is going to be a rather technical post, but even if you are non-tech and you bear with me till TLDR at the end, you'll probably learn something new to protect your company's most prominent digital asset: the Domain name.
In this series, I'm sharing insights from one of my recent investigative cases involving corporate sabotage through DNS manipulation specifically, tampering with NS (Name Server) records. This tactic disrupted email communications and domain accessibility, raising serious questions about contract validity, liability, and preventive measures.
The twist? I'm no cybersecurity expert just a software guy who's been tinkering with digital forensics for over two decades. I first played with a Router's settings when I was 15, fast forward to today with AI tools accelerating investigations, the landscape is evolving rapidly and becoming even more fascinating. You can trust me, or not... 🙃
All events described in this article are made up events to illustrate the concepts, any similarities are coincidental.
🧨 The Sabotage Unfolds
Payment Promises and Delays: The client had repeatedly promised payment on a specific date, let's say December 18th, but the day came and went without any transfer or response.
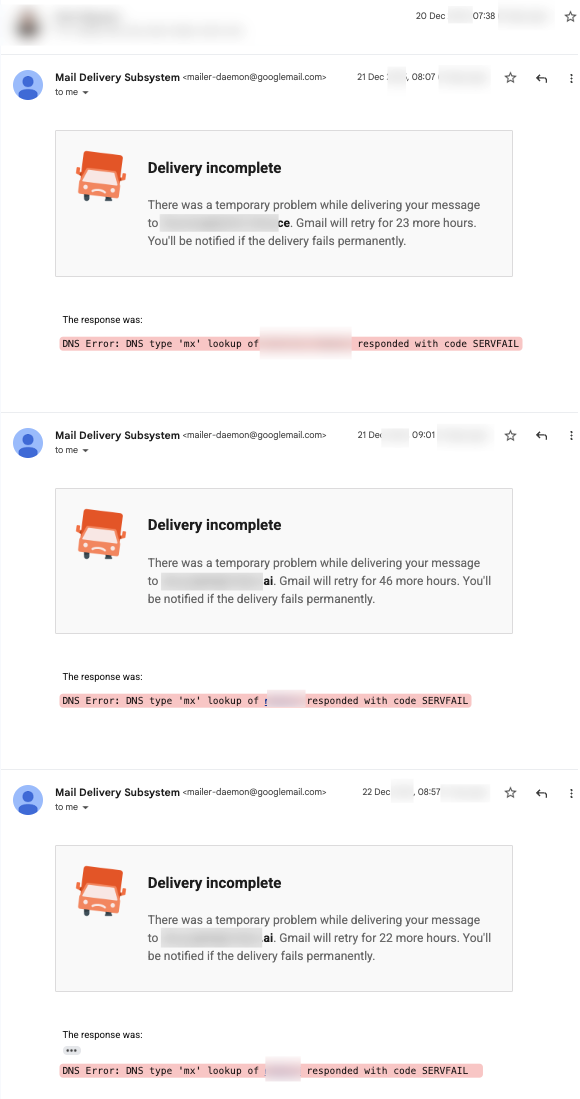
Communication Breakdown: I followed up via email on 20th, only to discover bounces back on 21st due to domain NS issues. This affected not just one domain but several under the client's control, suggesting that it is intentional (shown below).
Client's Evasive Response: On December 22nd, the client replied, claiming efforts to pay but providing no concrete timeline. Notably, they ignored the email failures, the domain downtime (which lasted several days), and even denied responsibility for payment on completed work, phrased it as charity help, not a contractual debt.
Unmentioned Downtime: The client never acknowledged the domain going "dark," which halted all email and web access temporarily.
This pattern screamed foul play, prompting a deeper dive!
🗃️ The Investigation
My curiosity led me to trace the timeline using reliable tools. Here's what DNS history revealed from dnshistory.org...
This story is for members only
Unlock the full archive containing deep dives into engineering culture, physical computing, and the realities of tech building. No password required.
Continue Reading
AIoT Coding
AI Minions and the New Operating System for Work
If you are still managing people the traditional way, you might already be falling behind the invisible operating system that is quietly running modern startups.
Leadership
Technology Is Real Power: The New Rules of Influence
We still pretend that politicians and legacy corporations run the world, ignoring the invisible digital rails where the actual power now resides.
AIoT Coding
Our servers were attacked on Vietnamese New Year 2026 by a Vietnamese Botnet - 18th Feb 2026.
How a forgotten caching database led to a major holiday outage, and why AI on the server saved the day.