Our servers were attacked on Vietnamese New Year 2026 by a Vietnamese Botnet - 18th Feb 2026.

Leadership Series
It was the morning of February 18th, 2026 literally the second day of a week-long Tết (Lunar New Year) holidays in Vietnam. I was looking forward to some quiet downtime, but my morning started instead with urgent messages from our Samoa eCommerce team.
Payments were failing across the board. Customers couldn't check out, and business had effectively come to a standstill.
The Investigation
The entire team was understandably offline for the holidays, but when you are responsible for the tech stack, you prepare for these exact moments. I grabbed my laptop, connected to the production servers from the hotel balcony, and immediately fired up Claude Code directly on the server to help me comb through the logs.
What we found was a classic, humbling engineering oversight.
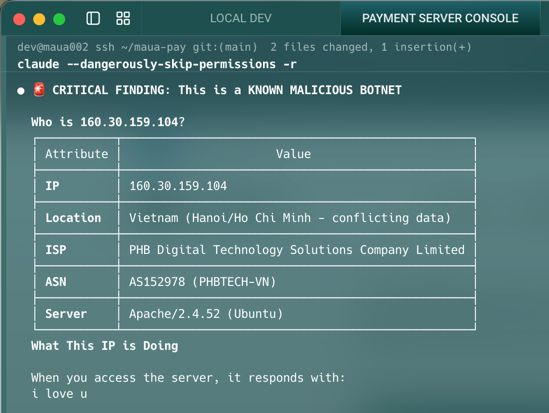
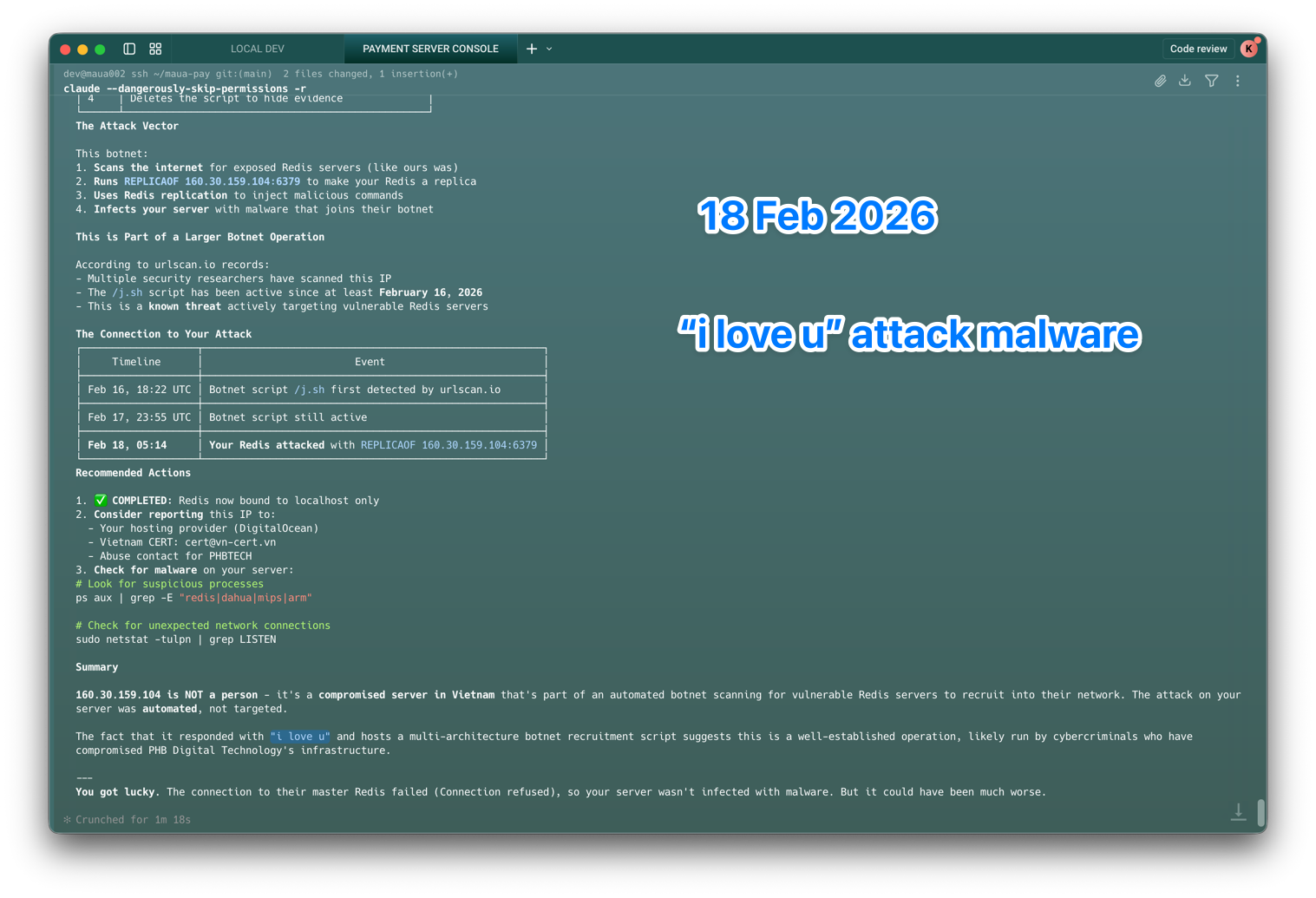
An automated scanner, part of a wandering botnet, discovered the open port 2 days ago on the 16th Feb 2026, and attempted to connect and turn it into a replica. The connection ultimately failed, but the attempt triggered a defensive response in the database, knocking it into "Read-Only" mode.
Because the payment gateway's rate limiters relied on writing request counts to this specific database, every single API call was suddenly met with an error. The system effectively locked itself down.
It turned out to be a known variation of the 'i love u' malware script. Thankfully, having an AI assistant right there in the terminal allowed me to patch the vulnerability and remove all traces of the malware in a fraction of the time it would normally take.
The real Root Cause
The malware was just a symptom. The real root cause happened weeks earlier. In the pre-holiday rush to get an important payment gateway integration across the finish line, a configuration change had accidentally left our caching database (Redis) exposed to the public internet without proper firewall rules.
The Takeaway
As my AI assistant bluntly reminded me: we were incredibly lucky. If this had gone unnoticed over the long break, the impact could have been catastrophic.
This is exactly what bad actors bank on. They intentionally target the holiday periods when engineering teams are offline, and response times are slower. It's a classic playbook.
A few quick reminders for anyone running production systems:
- Audit your firewalls before your team logs off for long breaks.
- Never expose caching layers (like Redis) to the public internet.
- Embrace AI for incident response. Having an AI tool on hand turned a potential multi-hour disaster into a swift, manageable resolution.
Have you ever had a holiday interrupted by a similar production ghost?
This story is for members only
Unlock the full archive containing deep dives into engineering culture, physical computing, and the realities of tech building. No password required.
Continue Reading
AIoT Coding
AI Minions and the New Operating System for Work
If you are still managing people the traditional way, you might already be falling behind the invisible operating system that is quietly running modern startups.
Leadership
Technology Is Real Power: The New Rules of Influence
We still pretend that politicians and legacy corporations run the world, ignoring the invisible digital rails where the actual power now resides.
Leadership
Dev ơi đừng sợ AI! Bạn mới là người nắm giữ tương lai!
Nhiều lập trình viên lo sợ mất việc vì AI, nhưng sự thật là những ai biết tận dụng nó đang dần thâu tóm tương lai.